I have tried to use Parted Magic on a live USB but when it goes into the OS there mouse does not work, even if I happen to get to Erase disk using just the keyboard the SSD is in a frozen state and I cannot seem to get it to unfreeze. I am not sure how I can use TRIM in Windows to erase the SSD either as the SSD is the only drive in the system and has Windows installed on it.
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Want to Sell Reminder: Properly Wipe Storage Devices Before Selling
- Thread starter SKYMTL
- Start date
- Location
- Edmonton, AB
Using "full format" in Windows to wipe a data storage only drive doesn't wipe everything? Thought it did...
There are ways to recover data off a drive fairly easily if you just do an ordinary format.
I just formatted the partition on the SSD by removing it from the machine and adding it via a dock to another machine and then going into disk management and formatting it. As the other PC has TRIM active then this should be fine right?
If you look at my posts, you'll see I like messing with drives as much as I do overclocking, so hmm let's try it! [TL;DR - TRIM beats a Piriform Recuva scan, but I'm still not trusting it if there are more proven techniques that take just a little more time.]
I'll use Piriform Recuva to try to get the data back - yes there are more complex methods, but its easy to use. If you know you're under attack by something significantly more complex (e.g. laboratory), then why isn't every disk you own encrypted?

Test setup:
Windows 10 Pro updated as of today
The drive with TRIM: AMD R3SL480G SSD (although I'm using a 2 GB partition because I'm lazy and don't want to full format the entire drive and waste a write cycle)
The drive with no TRIM: A 4 GB SD card plucked from a Nintendo 3DS
Partition type: FAT32
I'm using FAT32 for the filesystem because it's faster to recover from without all those journalling bits that NTFS has.
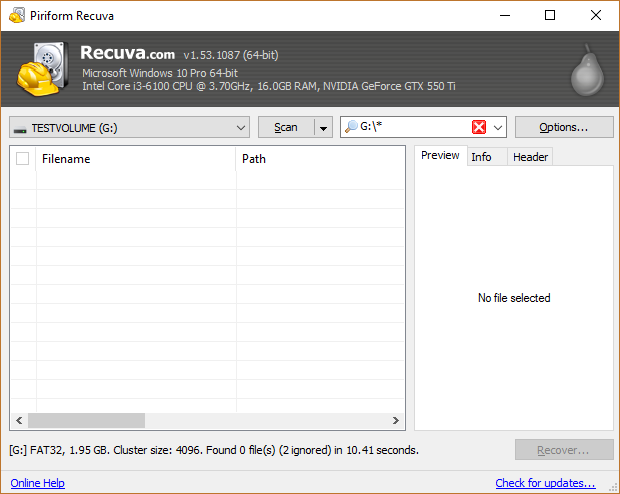
Here's what Recuva tells me for a volume that just got a full format (although I'm not sure if that bit of my SSD even had stuff on it to begin with).
For this test, each drive will contain "classified document" (docx), plain text passwords - real passwords by the way (txt), and "pr0n" (jpeg) - ten copies for each item.
To start the test, I used a full format through Windows.
First off, I'll start with a "control" test on a device that definitely doesn't have TRIM - a 4 GB SD card!
Here's what I start off with:

Now I QUICK format it.

Recuva seems to find the old contents of the files rather quickly, with 24 results almost immediately after starting the tool.

After it finished, it looks like Recuva only got the DOCX and the JPGs back. That's not to say plain text is unrecoverable! (e.g. you'd get it back quickly if you do a search for UTF-8 or ASCII encoded words in English)
 recuvaresults
recuvaresults
Now let's check the contents of the files...


Yup! The "pr0n" is there in all its glory, and the typo in the document is also still there.
So now for the SSD partition. I started it off with the same files as the SD card.
Now Quick Format, then Recuva similar to the first drive...
DISCLAIMERS:

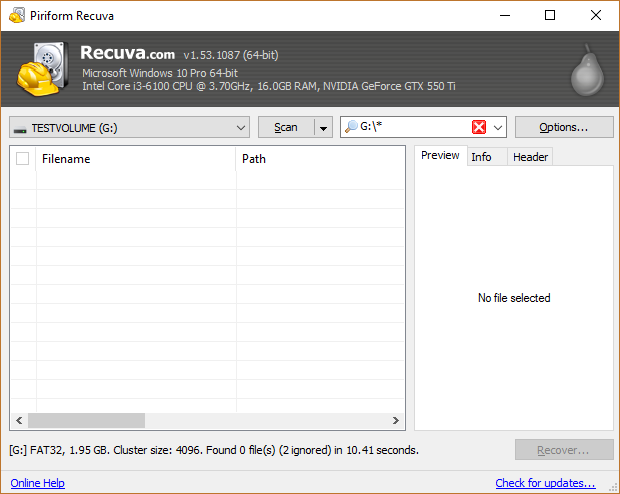
Recuva can't find anything on the QUICK formatted SSD partition.
The result surprised me a bit that Windows TRIMed the drive so quickly, but still I'm too paranoid.
I just make heavy use of AES-NI available in CPUs these days and Veracrypt / Bitlocker everything. (That also saves me from worrying if I RMA a drive and hope that Seagate / WD's partners are not collecting my secrets.)
If I do want to wipe a drive for whatever reason, I usually use the hdparm command line tool with Linux and issue an internal secure erase (ISE) instruction. (An ISE is much faster on SSDs than an overwrite with random / zeros.) If I'm using a drive or computer that's incompatible with ISE (USB enclosure, laptop that doesn't have the right Linux drivers, etc), I'll use copywipe on Windows or Shred on Linux to do a pass with random values.
I'll use Piriform Recuva to try to get the data back - yes there are more complex methods, but its easy to use. If you know you're under attack by something significantly more complex (e.g. laboratory), then why isn't every disk you own encrypted?

Test setup:
Windows 10 Pro updated as of today
The drive with TRIM: AMD R3SL480G SSD (although I'm using a 2 GB partition because I'm lazy and don't want to full format the entire drive and waste a write cycle)
The drive with no TRIM: A 4 GB SD card plucked from a Nintendo 3DS
Partition type: FAT32
I'm using FAT32 for the filesystem because it's faster to recover from without all those journalling bits that NTFS has.
Here's what Recuva tells me for a volume that just got a full format (although I'm not sure if that bit of my SSD even had stuff on it to begin with).
For this test, each drive will contain "classified document" (docx), plain text passwords - real passwords by the way (txt), and "pr0n" (jpeg) - ten copies for each item.
To start the test, I used a full format through Windows.
First off, I'll start with a "control" test on a device that definitely doesn't have TRIM - a 4 GB SD card!
Here's what I start off with:

Now I QUICK format it.

Recuva seems to find the old contents of the files rather quickly, with 24 results almost immediately after starting the tool.

After it finished, it looks like Recuva only got the DOCX and the JPGs back. That's not to say plain text is unrecoverable! (e.g. you'd get it back quickly if you do a search for UTF-8 or ASCII encoded words in English)
 recuvaresults
recuvaresultsNow let's check the contents of the files...


Yup! The "pr0n" is there in all its glory, and the typo in the document is also still there.
So now for the SSD partition. I started it off with the same files as the SD card.
Now Quick Format, then Recuva similar to the first drive...
DISCLAIMERS:
- The fact that this one tool fails only tells you it's harder to recover stuff, not that it's impossible to recover stuff.
- This all hinges on TRIM working! Problems with drivers, USB enclosure not supporting TRIM, etc., will leave the SSD in the same state as my SD card after a quick format. On this item alone I personally won't risk it.
- This is nowhere near conclusive! (e.g. I'l probably have to do a low-level read to see what the drive actually reports)

Recuva can't find anything on the QUICK formatted SSD partition.
The result surprised me a bit that Windows TRIMed the drive so quickly, but still I'm too paranoid.
I just make heavy use of AES-NI available in CPUs these days and Veracrypt / Bitlocker everything. (That also saves me from worrying if I RMA a drive and hope that Seagate / WD's partners are not collecting my secrets.)
If I do want to wipe a drive for whatever reason, I usually use the hdparm command line tool with Linux and issue an internal secure erase (ISE) instruction. (An ISE is much faster on SSDs than an overwrite with random / zeros.) If I'm using a drive or computer that's incompatible with ISE (USB enclosure, laptop that doesn't have the right Linux drivers, etc), I'll use copywipe on Windows or Shred on Linux to do a pass with random values.
Times are a changing 
I have read that ssd's like to shuffle data around, and therefore using a traditional zero wipe or even dod method is questionably effective.
The only method I have found that is currently recommended by professionals is the internal ata secure erase.
So if you are using Dban for ssd's you might want to reconsider, or even better use Dban in conjunction with drive encryption and secure erase, why put all your eggs in one basket? Dban/external wipe seems to also be rougher on ssd's in regards to write lifetime, secure erase appears to take advantage of drive encryption on ssd's rather than wiping data, and therefore takes about 10 seconds on ssd's.
Parted magic offers both internal (secure erase) and external drive erase methods, the relative user friendliness will cost you ~10$ though.
This is all just iffy information anyone can read on the net so take it with a grain of salt
I have read that ssd's like to shuffle data around, and therefore using a traditional zero wipe or even dod method is questionably effective.
The only method I have found that is currently recommended by professionals is the internal ata secure erase.
So if you are using Dban for ssd's you might want to reconsider, or even better use Dban in conjunction with drive encryption and secure erase, why put all your eggs in one basket? Dban/external wipe seems to also be rougher on ssd's in regards to write lifetime, secure erase appears to take advantage of drive encryption on ssd's rather than wiping data, and therefore takes about 10 seconds on ssd's.
Parted magic offers both internal (secure erase) and external drive erase methods, the relative user friendliness will cost you ~10$ though.
This is all just iffy information anyone can read on the net so take it with a grain of salt
- Location
- Moncton NB
I'm sure AkG will chime in, but my initial understanding was that doing a zero wipe / dod (major pita on slow mech drives........  ) on an SSD is actually bad for the SSD. Writing multiple passes of ones and zeros is something required by mechanical media whereas SSDs are simply electrical binary states as opposed to recordings of those binary states that might have some persistence. If you flip an ssd's bits all to zero with a secure erase function (including the cache) there should be no way to recover the information.
) on an SSD is actually bad for the SSD. Writing multiple passes of ones and zeros is something required by mechanical media whereas SSDs are simply electrical binary states as opposed to recordings of those binary states that might have some persistence. If you flip an ssd's bits all to zero with a secure erase function (including the cache) there should be no way to recover the information.
- Location
- Grande Prairie, AB
HDDerase that I posted about on the first page should still work w/ doing a secure erase on an SSD. You will need to set SATA to IDE compatible mode. If HDDerase detects the drive as 'frozen', just unplug the power and SATA cable. Wait a few seconds. Then plug them in. Should be good to go.
xentr_legal_notice_title
xentr_legal_notice_description
